Rootcon is a security conference held annually in the Philippines and it was on its 13th iteration this year. Josef, one of our engineers, is from the Philippines and aside from Python and Raspberry Pies, security is one of his areas of interest. Rootcon 13 has long been in Josef's calendar and now that the event has concluded, he has some thoughts to share.
Security is one of those areas where continuous learning and improvement is essential. it's a domain where the truth in the adage "knowledge is power" is realized in many ways. And when we stop learning, the rest of the world leaves us behind. This is applicable in many places, but it's especially so in security.
Attackers and defenders are always one-upping one another and it's really hard to catch up with everything happening. In the computing landscape where hardware, software and people interact, there are a lot of weaknesses for malicious actors to find and exploit.
I've been to Rootcon twice, and both times, I feel that the talk topics can vary very widely, which is very different from other conferences where you can somehow link or relate topics to each other. This just goes to show how broad the field is and how people can come from very different specializations. I consider myself a security enthusiast and in my attempt to make sense of all of this, here are some general thoughts developing in my mental map with regards to security.
Hardware
We hear security people say that hardware manufacturers aren't giving enough to secure the devices they create. Let's forget for a moment all the unsecured devices that are connected to the internet, the misconfigured devices or devices with default credentials deployed in a lot of places. Even if security measures have been taken, physical access to a device spells "game over" for many of them. If physical access can't be secured, there's also some that have wireless access, which further opens up a lot of possibilities for others to exploit. Nowadays we see more and more "smart" devices in our homes and offices, increasing the surface area that attackers can take advantage of.
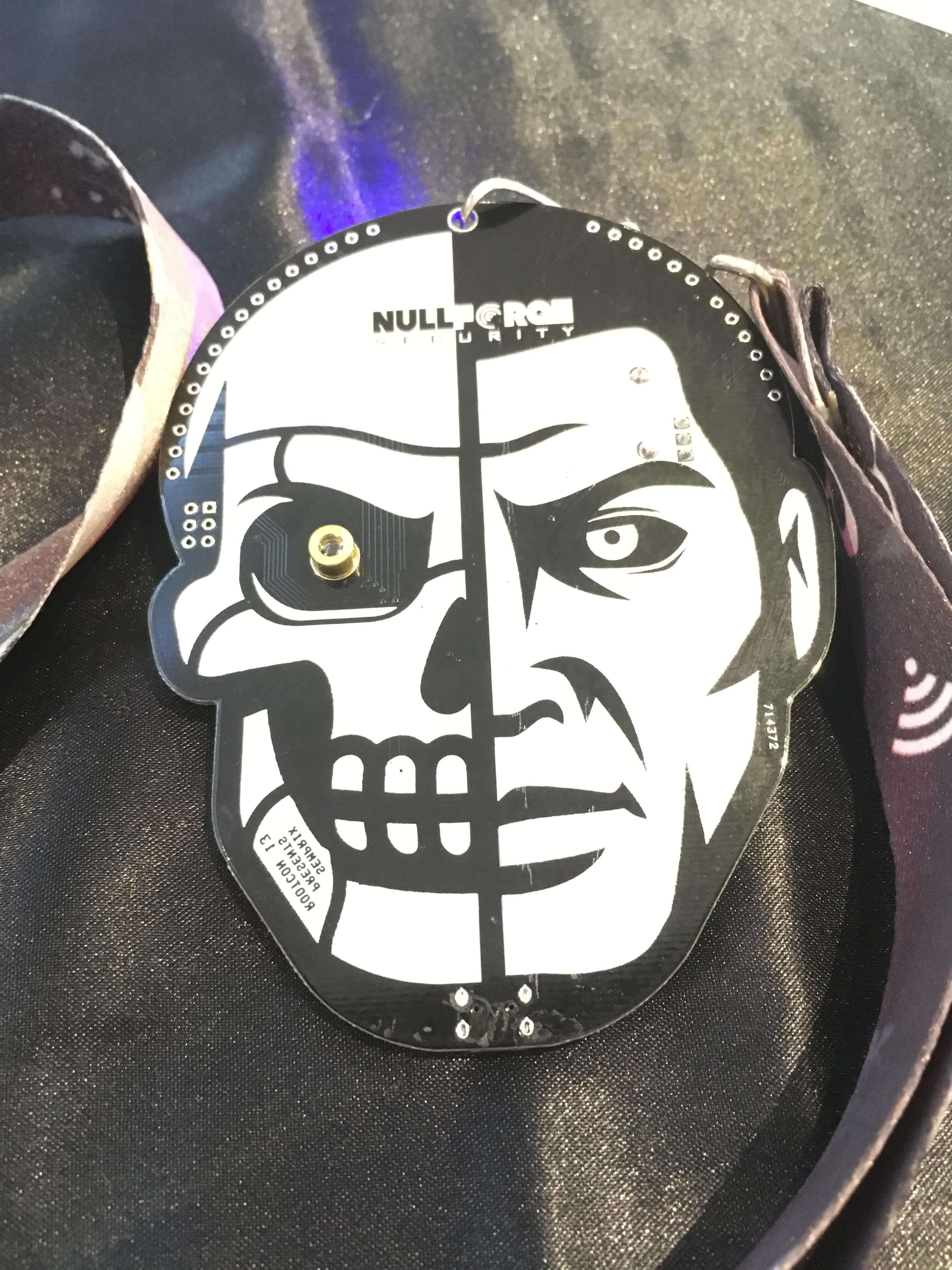
In this year's rootcon, there was a car hacking village demonstrating a device that connects and manipulates a car's dashboard using a game controller. So not only do we think of security in our homes and offices, our methods of transportation are also getting targetted. Aside from the car hacking village, there was a hardware hacking village where people could solder their own badge, and I seem to have spent a little too much time hanging out in the lock-picking village...
Software
Software is changing at a very fast pace. As someone in this line of work, I experience this everyday. We hear security people say that software developers don't think about securing their (our) applications enough. Aside from the software we write, there's software we rely on, software written by others. This occurs on many levels: it can be some third-party library, package, another application, the OS or even external services we're using. It's every other code that surrounds it. Thanks to this, we don't have to reinvent the wheel. It makes creating other software faster and easier, but it also opens up our software to potential vulnerabilities not only because of what we wrote but because of what others wrote!
With all the code we rely on, it may be just a matter of time when a vulnerability suddenly appears in any of them. The flip side to this is we don't have to use the latest tech all the time. Latest doesn't necessarily mean stable and secure. We have a choice between possibly old and unpatched or latest and unstable, both can be equally vulnerable.
In the end we have to strive for balance. We need to keep on updating and moving forward with technology, but keep things stable. But we can't slack off, it relies on the choice of software we use and how fast we can keep ourselves updated so that we can also make proper updates or changes to our software, fix bugs and patch holes.
Here's a more thorough article discussing software dependencies and reuse.
People
In the end, people still play a very important part of the whole system. Not only do we need to constantly update our software and hardware but also our people-ware. We, "IT/tech people", need to constantly update our knowledge of the potential threats that may affect our systems. New threats are constantly discovered while the "normal users" usually remain oblivious. This lack of awareness is one of those things that are taken advantage of by attackers. People "get hacked" too.
To guard against social engineering, we need to educate ourselves and the average users with the proper knowledge to defend themselves. This will help not only in securing the company but their personal lives as well. As new threats are discovered and the usual social engineering tactics become less effective, attackers can also get creative with their methods. We should arm ourselves with information faster than the attackers can take advantage of it.
Looking back at these reflections, I seem to have developed a grim outlook on things. And that my solution would be for every person to become half a security professional, especially for those in tech. It's just not possible and not practical.
As for me, I've decided some time ago to dedicate some time to learn more about security and that is the reason why I always try to attend this conference. We should always be learning.




